Technology
Securing Your Desktop
In todays computing environment, the security of all computing resources, from network infrastructure devices to users desktop computers, is essential. There are many threats to users computers, ranging from remotely launched network attack to malware and viruses that are spread through e-mails,...
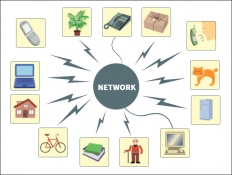
UBIQUITOUS PROMISES: Internet of Things
Human civilization over time devised various ways to communicate and interact with one another through the means of postal/telephonic/Internet based communication. Present world is enjoying all time connected phenomena, riding on the successful implementation of Internet and Internet based technology....
RESPONSIVE WEB DESIGN: Device Friendly Web Viewing
India is a fast growing market for internet users. Technological innovations and availability of new handy devices help people to access internet more on their smart phones, tablets, net-books and other such mobile devices than the desktop PCs. Nowadays, every website owner wants a mobile version...
eOffice Knowledge Management System
eOffice KMS is a simple, easy to use and rich feature, browser based document management system. It transforms both paper and electronic documents into knowledge assets that can be instantly used by the organization workforce.
OPEN SOURCE HARDWARE- An Emerging World of Opportunities
The IT world is witnessing phenomena of a kind due to massive availability of open source software, which has become an important part of software development process and has given people a wide range of choices and benefits. On parallel lines, the same is being conceptualized in hardware field also,...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


