Technology
POWERING GIGW COMPLIANCE
In the last decade or so, India has metaphorically witnessed a lot of water surge & not just meekly flow under the bridge. Technology has played an increasingly prominent role as enabler and leveller. Enabler- Technology continues to bring a flood of opportunities to lead lives very differently...
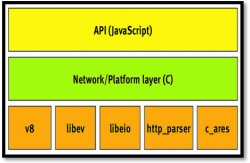
NODE.JS: Lightweight, Event driven I/O web development
As number of internet users is rising steadily, the servers are getting flooded with their requests and responses. To advert this situation, the servers are highly equipped with the high-end hardware like maximum number of core/processor, memory, enhanced I/O devices etc. But, these arrangements...
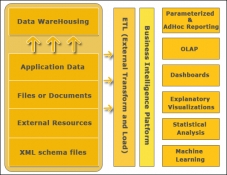
BIG DATA ANALYTICS
and the endless possibilities that it promises in all spheres of life has led to the coining of the term Big Data. Gartner defines Big Data as high volume, velocity and variety information assets that demand cost-effective, innovative forms of information processing for enhanced insight and decision making....
GoI Search as a Service (GoI-SaS)
Government of India (GoI) Search Platform initiative has enabled the citizens and other stakeholders to quickly access the data on Government websites. Under this initiative, Search as a service (GoI-SaS) facilitates the website owners in the Government to define their own search interface...
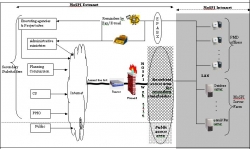
INFRASTRUCTURE PROJECT MONITORING SYSTEM OF MoSPI
Infrastructural development mirrors the overall health of a nation economy. This is particularly true for developing economies where investments in infrastructure development lead to growth, life improvement and poverty alleviation. India has invested heavily on infrastructure development and...




 Subscribe
Subscribe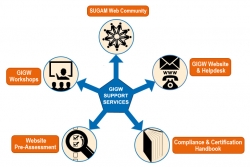


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


