Technology
National Cloud Services of NIC
With the emergence of Cloud computing and its power to foster efficiency in Governance, there has been a paradigm shift in the setting up and management of ICT services in Indian Government. Through Cloud services, the provision of ICT infrastructure to various departments and organizations of...
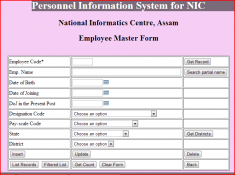
APPBUILDER:A Tool & A Framework
Software developers quite often come across situations where fast prototyping of a software becomes absolutely essential. Most of these software are database-centric and CRUD (create, retrieve, update, delete) functionalities form about 30%-40% of the total development effort (if not more)....
National Cloud Services of NIC
With the emergence of Cloud computing and its power to foster efficiency in Governance, there has been a paradigm shift in the setting up and management of ICT services in Indian Government. Through Cloud services, the provision of ICT infrastructure to various departments and organizations of...
Achieving High Availability of Databases through Failover Clustering for databases using Microsoft SQL Server 2008
One of the major challenges which IT systems face today is System Availability. Availability is critical in terms of components viz., Web Server, Database Server, and Network. Without availability, services fail, SLAs exceed, revenue is lost and finally a bad publicity can leave a lasting effect...
LINKED DATA: Road to Intelligent Web
Linked data is emerging as a new paradigm for publishing and interlinking data from different data sources and evolving web from Web of linked documents into the Web of linked data. The global database created by linked data provides flexible interorganizational collaboration and dynamic...




 Subscribe
Subscribe
.jpg)



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


