Technology
e-Pothi: Online Manuscripts Cataloguing System of Odisha State Museum
Odisha is known for its rich cultural heritage, monuments and palm & bamboo leaf manuscripts. The State Museum is unique in the Country, having rare & other forms of manuscripts. e-Cataloguing system (e-Pothi) has its genesis in fulfilling intellectual requirements of research scholars...
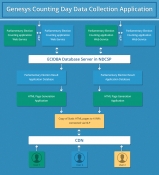
Collection, Consolidation and Dissemination of Results of General Elections 2014 using ICT Tools
India is the largest democracy of the world. Considering vast geographical expanse and large size of electorate, carrying out free and fair election process in India is quite complex and challenging. With 814.5 million registered voters taking part, General Elections 2014 have proved to be biggest...
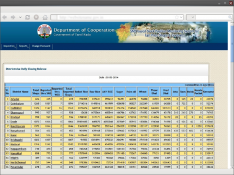
SMS BASED MONITORING SYSTEM FOR FAIR PRICE SHOPS IN TAMIL NADU
The Co-operation, Food and Consumer Protection Department of the Government of Tamil Nadu has the operational responsibility of identification of beneficiaries, issuance of ration cards and supervision of movement and distribution of food grains from godowns through Fair Price Shops located all...
E-COURTS MISSION MODE PROJECT IN MANIPUR
The implementation of e-Courts in Manipur has resulted in the setting up of 14 ICT rooms/ Judicial Service Centres at 12 court complexes, providing a range of services including generation of Cause lists, availability of judgments, viewing of case status, availability of digitally signed copies...
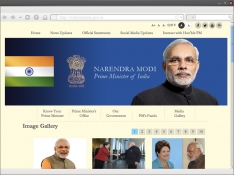
Launch of Prime Minister's Website
Just seconds after Shri Narendra Modi was sworn-in as the 15th Prime Minister of India, the official website of the Prime Minister of India http:// pmindia.nic.in/ was made live by NICs web development team with active support from NIC Cell at Prime Minister Office (PMO). Brimming with latest...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


