Technology
District Chamba, Himachal Pradesh
The IT revolution in Chamba kick started with the establishment of NIC District Centre in the year 1988 aiming at providing IT Support and Services to various Government and Public sector Departments. Since then, ICT has played a pivotal role in improving e-Governance and delivery of citizen centric...
Integrated Online Hotels Reservation System
The new Integrated Online Hotels Reservation System (iOHRS) developed by NIC, Himachal Pradesh is a standard solution to make the best use of Internet for providing improved services to tourists of Himachal Pradesh.
National Cloud Services of NIC-A successful journey towards Digital India
ClOUD manifests to be an effective way of provisioning ICT in-frastructure set-ups in government because of its cost effectiveness, agility and sustainability, which further ensures rap-id deployment & delivery of e-Governance projects and services.
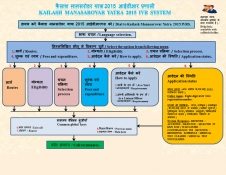
IVRS@NIC: Kailash Mansarovar Yatra (KMY) 2015
NIC TDPP division IVRS has been an integral part of the telephony revolution that the country has witnessed since the last decade. Right from the challenging period of analog cards and C++ codes interacting with card API for creating a call flow in the late 90s, the IVRS evolved to GUI Call-flow Management....
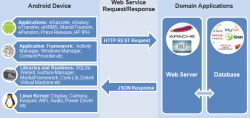
Android Mobile Apps to Supplement Web Content
India has the fastest growing telecom network in the world credited to its high population and development potential. The total number of telephones in the country stands at 957.61 million, while the overall teledensity has increased to 76.75% as of 30th September 2014. The total number of mobile...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


