Technology
Ujjwala-Textual and Demographic De-duplication
India is widely touted as an emerging economic power, but nearly half of the country still cooks with firewood. According to 2011 census, only 28.5% of the 1.3 billion population across India uses LPG/ PNG for cooking. Pradhan Mantri Ujjwala Yojana (PMUY) aims at providing 5 crore free LPG connections...
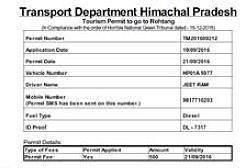
Online Rohtang Pass Permits Issuance System
To make it easier for the Rohtang Pass commuters, the payment gateway has been integrated with the system so that all the charges can be paid online and the permit is issued on successful receipt of payment by the Department. This web application is a unique mode of getting permits.
Employee Online App
In near future, the 'Push Notification' service of EO App will be decoupled and provided as a component or a web service so that it can be resused by other applications.
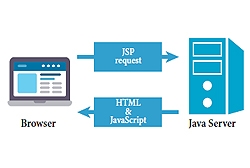
Java Help System
The JavaHelp System allows users to access the help files and topics for the CollabCAD software from their desktop or their browser application without necessarily having to install the CollabCAD software. It allows for easy access to help for beginning users and a quick reference guide for the more...
Online Consent Management and Monitoring System of JSPCB
Jharkhand State Pollution Control Board (JSPCB) has taken various initiatives during past year and a half, with the objective of 'Ease of Doing Business' in the State for transparent and expeditious decision making.




 Subscribe
Subscribe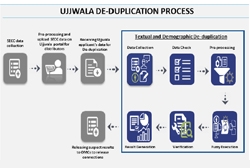

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


