Technology
JEEVAN PRAMAAN Digital Life Certificate
Since its implemention in 2014, over 1.6 crore DLCs have been submitted by over 90 lakh pensioners. 3.01 lakh DLCs were submitted in a single day on 13th Nov, 2017. Peak utilization of the system was observed as 1,205 DLCs per minute on 9 Nov, 2017 at 11:36 AM. Jeevan Pramaan ecosystem has...
e-HRM System for Government by NIC
This recently launched Application enables creation of e-Service book of employees from physical service book and automate the updation of e-Service book. This makes day-to-day processing of various records of employee possible, resulting in real time updation of servicebook and uniform implementation...
Online GPF System of Arunachal
Catering to the need of Directorate of Accounts and Treasuries by incorporating all the features required for maintaining GPF accounts and generating all essential reports and statements, the online GPF System follows a very transparent approach in providing a comprehensive resource of information...
PDF Digital Signing Tool 3.0
PDF Digital Signing Tool 3.0 has been built on latest technology using JavaFX with enhanced features, improved and intuitive signer interface. This new version facilitates digitally signing of the electronic documents (pdf) by reading Digital Certificates (X.509) from USB token provided by the...
e-Granthalaya- Transforming Traditional Library to e-Library with Automation and Networking of Government Libraries
e-Granthalaya is a library management software facilitating automation of in-house activities of library as well as member services. This web-based and cloud-ready application is used online by the member libraries for data entry, return of issues and other key member services. The Software is hosted...




 Subscribe
Subscribe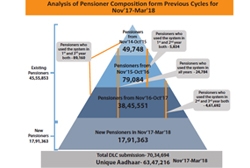




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


