Technology
Suraksha Suite of Arunachal - Enabling Arunachal Pradesh Police to spot and reach out to distressed citizens & tourists
Ensuring safety of its citizens is one of the prime responsibilities of any government. The Arunachal Pradesh State Police is the arm of the government to take timely measures to ensure adequacy of security and safety of the public. It is with such an intent, the Arunachal Pradesh Police has entrusted...
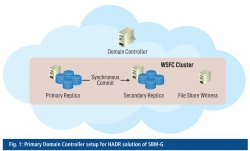
Swachh Bharat Mission - Gramin, Ensuring High Availability, Disaster Recovery and Design Implementation
The Swachh Bharat Mission -Gramin (SBM-G) programme, under the Ministry of Drinking Water and Sanitation, is a flagship programme of the Government of India. The e-Governance application used for its monitoring has been developed in-house by NIC under the guidance of the SBM-G programme division.
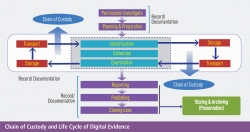
Digital Forensics - Paving the way to preserving evidences critical to decisions in cybercrime investigations
We live in an era of digital revolution in which Information Technology touches day-to-day activities mankind delve in. The socio- economic fabric has been immensely benefitted by the IT intervention, and the judiciary is no exception to this. The penetration of IT in the legal ecosystem has created...
Appscape
Tapping the potential of advanced technologies, e-Governance provides services through the use of computerization and replaces traditional way of working with paperless work. Mobile governance (m-Governance) is a subset of e-Governance to deliver services for different government channels, namely G2C,...
e-NIYANTRAN : Online Time Card System to save the migrating wildlife of Kaziranga National Park, Assam.
e-Niyantran will replace the existing Manual Time Card System of regulating the vehicular movement on NH-37, the highway which runs parallel to the southern boundary of Kaziranga National Park. The system would help avoid accidental death of wild animals while they cross the highway, especially during...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


