Technology
Chatbot Framework for e-Gov : Meet VANI - Virtual Assistant of NIC
VANI is a virtual assistant that mimics a human & tries to help users - especially those not well versed with the web or technology in general. It is built using the principles of the latest disruptive technology of our times, that is Machine language & artificial Intelligence.
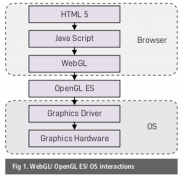
WEBGL AND THREE.JS : 2D/ 3D graphic rendering Javascript API
WebGL (Web Graphics Library) 1.0 is one of the Javascript APIs for rendering interactive 3D and 2D graphics within any compatible web browser without the use of plugins. There are many Javascript libraries that abstract WebGL and result in higher code level. One of the utility libraries is Three.js,...
DSC SIGNER : A cross-platform, browser independent plugin-free Digital Signature Solution
DSC Signer is a cross-platform, browser independent solution for digital signature using DSC tokens. The DSC Signer comprises of two components namely a client-based component and server-side API. DSC Signer solution is supported in all the major operating systems viz Windows, Linux and MacOS.
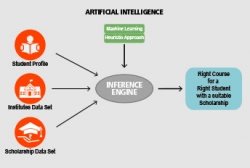
Right course for a right student With a suitable scholarship too : an AI approach
The possibilities are endless with the development of Artificial Intelligence based tool which can help and guide the students in selecting the suitable branch of higher studies in their area of interest to achieve their career objective.
LOHIT District, Arunachal Pradesh
The IT revolution in Lohit started with NIC, Tezu as one of the main wings of District Administration. Today it has become invaluable for District Administration to execute the various e-Governance and ICT activities in line with the Digital India Program of Government of India.




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


