Technology
Direct Benefit Transfer - Supporting the financial Institution of the government during the crisis of COVID-19
Direct Benefit Transfer (DBT) plays an important role during the crisis times to provide sustenance to the highly effected population such as farmers, daily wagers, migrant labours etc. by transferring cash benefits directly to their bank accounts as well as delivering in-kind benefits such as...
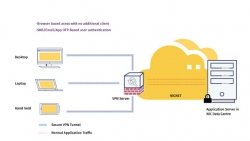
Virtual Private Network Services - Technology that enabled the government to work-from-home
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. Applications running across a VPN may therefore benefit from...
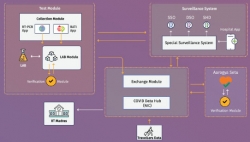
Integrated Core COVID-19 Management Framework - Ensuring availability of data across systems for better management of COVID-19 crisis
Corona virus pandemic has spread across the world at a fast pace disrupting life in unprecedented ways. Government of India has taken multiple measures like nation-wide lockdown, identification of hotspots/ containment zones, isolating patients and suspects, contact tracing, surveillance besides...
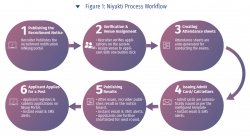
Niyukti - A one stop recruitment solution for the Government of Assam offered as a service
Since its inception in the year 2017, Niyukti has quickly evolved as a widely used recruitment solution in Assam Government. Its USP lies in the fact that it is offered as a service to the recruiting agencies, thereby allowing them to quickly onboard with a recruitment process in no time. Already...
Gujarat CM Dashboard - Enabling government machinery for strengthening good governance
The system first of its kind was an innovation in terms of accessing data from all e-Governance applications of the State of Gujarat and providing the same for monitoring against defined KPIs. In the reverse, CMO could drill down to the granular level on the fly for red-flagged items and intervene...

 Subscribe
Subscribe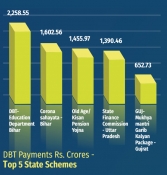


 Flipbook
Flipbook PDF (6.8 MB)
PDF (6.8 MB)