Technology
RT-PCR App - Mobile Application for Containment and Monitoring Covid-19 pandemic across the Country.
Covid-19 pandemic in India is part of the worldwide situation of coronavirus disease and a large number of people is likely to be affected by the coronavirus. The country has imposed initial lock-downs, supplemented by increased testing of people and contact tracing of patients as effective measures...
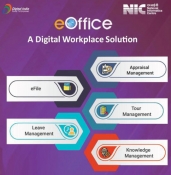
eOffice - A digital work place solution for Working From Home during COVID-19 pandemic
During the period of lockdown necessitated by COVID-19, work from home became the new mantra in public as well as the private sector. Governments whether Central or State, have traditionally followed a paper-based office. While the seeds of switchover to a less paper office were sown much earlier,...
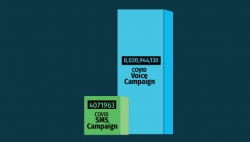
Messaging Services of NIC
During COVID pandemic, SMS service has seen a growth of almost 24% and has played a critical role in communicating with citizens
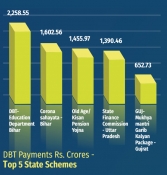
Direct Benefit Transfer - Supporting the financial Institution of the government during the crisis of COVID-19
Direct Benefit Transfer (DBT) plays an important role during the crisis times to provide sustenance to the highly effected population such as farmers, daily wagers, migrant labours etc. by transferring cash benefits directly to their bank accounts as well as delivering in-kind benefits such as...
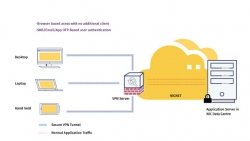
Virtual Private Network Services - Technology that enabled the government to work-from-home
A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network. Applications running across a VPN may therefore benefit from...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


