Technology
Integrated Core COVID-19 Management Framework - Ensuring availability of data across systems for better management of COVID-19 crisis
Corona virus pandemic has spread across the world at a fast pace disrupting life in unprecedented ways. Government of India has taken multiple measures like nation-wide lockdown, identification of hotspots/ containment zones, isolating patients and suspects, contact tracing, surveillance besides...
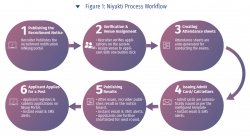
Niyukti - A one stop recruitment solution for the Government of Assam offered as a service
Since its inception in the year 2017, Niyukti has quickly evolved as a widely used recruitment solution in Assam Government. Its USP lies in the fact that it is offered as a service to the recruiting agencies, thereby allowing them to quickly onboard with a recruitment process in no time. Already...
Gujarat CM Dashboard - Enabling government machinery for strengthening good governance
The system first of its kind was an innovation in terms of accessing data from all e-Governance applications of the State of Gujarat and providing the same for monitoring against defined KPIs. In the reverse, CMO could drill down to the granular level on the fly for red-flagged items and intervene...
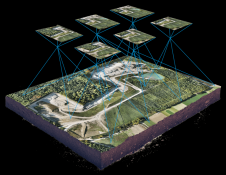
Changing the Paradigm of Mapping - UAV/ DRONE with AI/ ML Innovations
Drone enables topographic surveys of the same quality as highly accurate measurements collected by traditional methods, but in a fraction of time. This substantially reduces the cost of a site survey and efforts. Today drones coupled with Artificial Intelligence (AI) and Machine Learning (ML)...
Zero Trust Architecture - Framework to Strengthen Structural Security of Modern Enterprise
Zero Trust Architecture or ZTA is an infrastructure design philosophy based on the principle of 'never trust, always verify'. It debunks the typical 'castle-and-moat' style perimeter security and intends to handle newer threats of privilege misuse, internal breaches and lateral...




 Subscribe
Subscribe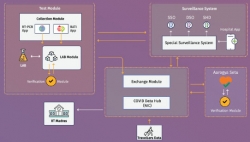



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


