Technology
AI Powered Cyberattacks A key technology in enterprise IT toolbox becoming a weapon of cybercriminals
AI-powered cyberattacks leverage AI and ML algorithms and techniques to automate, accelerate, and enhance various phases of a cyberattack. This includes identifying vulnerabilities, deploying campaigns along identified attack vectors, advancing attack paths, establishing backdoors within systems,...
Mitigating Cybersecurity Misconfigurations Exploring Common Cybersecurity Misconfigurations and Effective Techniques for Securing Digital Infrast
Cybersecurity landscape is an ever-evolving battleground in this age of rapid digital transformation. Organizations must stay one step ahead of adversaries to protect digital infrastructures effectively. The National Security Agency and Cybersecurity and Infrastructure Security Agency have...
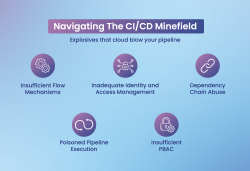
Securing CI/CD Pipelines Addressing the Unique Challenges in DevOps
CI/CD pipelines enable fast software delivery but come with security risks like weak flow control, IAM gaps, and dependency exploits. Mitigation includes role-based access control, multi-factor authentication, secure secrets management, and automated testing. Tools like Jenkins and GitLab CI/CD...
Tiruvannamalai, Tamil Nadu Explorer in e-Governance
NIC Tiruvannamalai pioneers dist- rict governance with innovative ICT solutions, significantly enhancing administrative efficiency and ci- tizen services. Through compre- hensive Government-to-Citizen (G2C) applications, it sets new standards in digital governance, ensuring seamless and effective access...
Securing Machine Identities with Multi-Factor Authentication Enhancing Security and Compliance in a Perimeter-less Network Era
Multi-Factor Authentication (MFA) for machine identities adds an extra layer of security by requiring multiple verification methods during authentication. This helps protect against cyber threats by ensuring that only authorized machines can access systems and data. Implementing MFA for machine...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


