Conference
General Elections 2024
Democracy is not just a question of having a vote. It consists of strengthening each citizens possibility and capacity to participate in the deliberations involved in life in society - Fernando Cardoso.
Budgam, Jammu & Kashmir Building Trust through Innovation
NIC Budgam has implemented many initiatives to enhance service / scheme delivery such as DIMP, SEEDS, e-Imprest, AurZuv, Covid19Exg, PRIS, Medical Migration portal, RozgarApp, TMIS, Meri-Aawaaz, BudgamStat, PMS, and CPMS which have transformed service delivery. Besides implementation of National...
Amritsar Punjab Setting a benchmark in delivering ICT Solutions to foster excellence
Home of the glorious Golden Temple, the iconic city of Amritsar, portrays the heroic character of Punjab. Taking the inspiration from the same, NIC Amritsar District Centre established in the year 1988 has implemented various eGovernance projects for State and Central Governments to leverage the eGovernance...
NextGen Technologies for Digital Government
Leading the conversation on the impact of ICT on Governments, NIC hosted the third edition of its TechConclave at Vigyan Bhawan, New Delhi, on the 3rd and 4th March 2022. Themed Next-Gen Technologies for Digital Government,the two-day event saw earnest participation of IT experts and industry leaders....
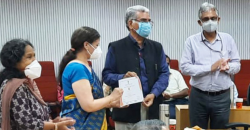
NIC TAG Awards and Launch Ceremony
NIC TAG group organised State Mobile App and WebApp UI/UX Contests in July 2021. The awards for these contests were presented by the Director-General, NIC Dr. Neeta Verma on 12th October 2021.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


