Elections
UDAIPUR: ICT Cruise at The City Of Lakes
Udaipur, the capital of the former princely state of Mewar, is a serene city located in Rajasthan and is famous world over for its lakes. Also known as the City of Lakes, Udaipur is one among the most romantic and beautiful cities of India.
Bhagalpur : e-Governance in the Silk City of Bihar
Bhagalpur, situated on the southern banks of the holy River Ganga, is famous for producing Tassar silk and sarees and hence also known as the Silk city of Bihar. The important places to visit are the ancient Buddhist University at Vikramshila, Jain Temple at Nathnagar, Sahjangi and the Ajagaibinatha...
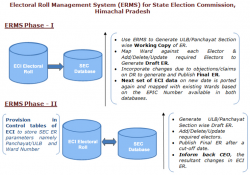
ELECTORAL ROLL MANAGEMENT SYSTEM (ERMS) FOR STATE ELECTION COMMISSION, HIMACHAL PRADESH
Electoral Roll Management System (ERMS) aims to leverage the use of voters data/electoral rolls generated by Election Commission of India (ECI) during Parliament and State Assembly elections for the purpose of Panchayat/ Urban Local Bodies elections, thus thwarting the duplicacy in...
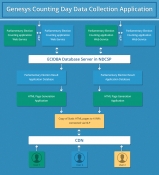
Collection, Consolidation and Dissemination of Results of General Elections 2014 using ICT Tools
India is the largest democracy of the world. Considering vast geographical expanse and large size of electorate, carrying out free and fair election process in India is quite complex and challenging. With 814.5 million registered voters taking part, General Elections 2014 have proved to be biggest...
HAMIRPUR: Bridging the Digital Divide
Hamirpur, one of the twelve districts of beautiful state of Himachal Pradesh, lies in the middle of the Shivalik Ranges. It is the states most literate district and well connected by roads. Majority of the people serve for defense forces thus popularly known as Veer Bhoomi. The district is...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


