Elections
RAJASTHAN- Celebrating Twenty Five Glorious Years
NIC Rajasthan is celebrating silver jubilee of its establishment this year. The celebrations have started and the long journey with ups and downs has been quite fruitful. Today with the efforts of team NIC, the state of Rajasthan is surging ahead as a leader in e-Governance and ICT development,...
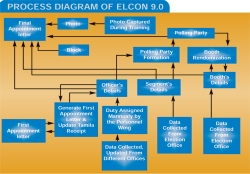
ELECON 9.0: Managing Assembly Elections in Bihar
Polling party formation, deployment of patrolling personnel, tagging of booths with the polling party, Electronic Voting Machines (EVM) randomization, vehicle allotment to the parties - all through random number techniques as per Election Commission of India (ECI) guidelines were made possible...
Information and Communications Technology in Elections in India
Conduct of Elections in India is an event that involves mammoth complexity and intensive planning considering electorate size, geographical spread and terrain of India. The advent of ICT in Indian Elections has once again underlined the fact, how technology is a boon to the entire mankind.The Election...
Bengal Assembly Elections: Utilizing ICT based Services
The recently concluded West Bengal Assembly Election- 2011 has once again underlined that ICT can be successfully employed in providing services towards management of election processes and activities.The various ICT based services, designed and developed by NIC Services Inc. (NICSI) in consultation...
Zunheboto : Providing ICT based Services & Support in Nagaland
Among the six districts of the Nagaland state, Zunheboto is situated in the middle bounded by Mokokchung in the East and Wokha district in the West. Tizu, Doyang and Tsutha - the three important rivers of the district are source for hydel power generation and terrace cultivation.High hills...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


