ICT Initiatives
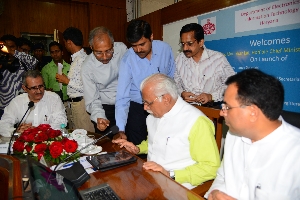
Punjab Chief Minister Mr Parkash Singh Badal launches eSuvidha (ePMS)portal as part of Digital India week to fast track stalled projects, on 2nd July 2015
Partaking in 'Digital India' week, Punjab Chief Minister Parkash Singh Badal launched the state Portal ePMS (Electronic Projects Management System) to fast track infrastructural development on 02.07.2015 at 09:30 AM in the CM Residence. The project was kicked off to enhance efficiency,...
eSamikSha did great job in Nepal Mission Success
eSamikSha played a seminal role in India’s gigantic rescue and relief mission in Nepal and India after the April 25 earthquake, which has been a big success by all accounts. The rescue and relief operation in the aftermath of the devastating earthquake was incessantly monitored at the highest...
Rail-eSamiksha Success Story : Railway Ministry Implements 39 budget announcement
The Minister of Railways Shri Suresh Prabhakar Prabhu launched ‘eSamikSha’ for monitoring the implementation of budget announcements/commitments, at a function held at Rail Bhawan on 21st April 2015. After the few days of the launch, The Ministry of Railway said it has implemented 39 announcements...
Haryana: Mobile App Launched for CM Windows (Grievance Recording & Redressal System) Status Tracking by Haryana Chief Minister on 2nd May, 2015.
The CM’s Window for recording & redressal of public Grievances has been functioning very well across the state, since its launching by the Chief Minister. The citizen can track the status of their grievance application through Internet from anywhere anytime. To further facilitate the...
Training Session on On-line Monitoring and Compliance Mechanism (Rail-eSamikSha) at Conference Hall, Ministry of Railway on 29th April 2015
eSamikSha, an online Monitoring and Compliance Mechanism has been developed by Cabinet Secretariat Informatics Division, to fast track the compliance of pending action points, proposal, targets, etc. of Various Ministry/Department/Organization/Agency of Govt. of India and Government...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


