Haryana: Mobile App Launched for CM Windows (Grievance Recording & Redressal System) Status Tracking by Haryana Chief Minister on 2nd May, 2015.
Neeraj, Haryana
s[dot]neeraj[at]nic[dot]in
| May 4, 2015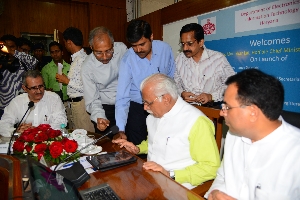

The CM’s Window for recording & redressal of public Grievances has been functioning very well across the state, since its launching by the Chief Minister. The citizen can track the status of their grievance application through Internet from anywhere anytime. To further facilitate the citizens, a Mobile Apps has been developed by NIC- Haryana at NIC-DIC Hisar. This Mobile Apps can be downloaded and used on any android based mobile phone.
This Mobile App has been launched by CM on 2nd May, 2015. The App is available for download from Google Apps Store, free of cost.




 Subscribe
Subscribe
 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


