Awards
NICSI Celebrates its Silver
National Informatics Centre Services Inc (NICSI) celebrated its Silver Jubilee on 28 Jan 2021 at a formal event at Vigyan Bhawan, Delhi.
Akola District - Pioneer with excellence in digital governance at the Cotton City of India
NIC, Akola is a pioneer with excellence in digital governance, with communication facilitation, technical support, system analysis, and innovative implementation of ICT. NIC, Akola is recognized with more than twenty various types of awards and recognitions for innovative initiatives...
The Digital India Awards 2020 ceremony
The Digital India Awards 2020 ceremony (sixth edition) took place virtually on 30th December, 2020 and the awards were conferred by the Hon'ble President of India, Shri Ram Nath Kovind from Rashtrapati Bhawan via video conferencing (VC), in the presence of Hon'ble Union Minister of Law...
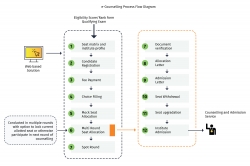
e-Counselling Services
e-Counselling services developed by NIC are the result of a focussed effort to put the best use of technology for bringing transparency in the admission process of the educational institutions in our country. This has also led to the implementation of a common selection process across...
Tech Conclave' 20 - Technologies for nextgen governance
Held on 20th & 21st January 2020, the yearly techno-event of NIC was power packed with inspiring talks and deliberations by eminent IT experts and techno-leaders from industry.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


