Cyber Governance
Screen Readers and designing Accesible Websites
It is responsibility of every website developer to ensure designing "Barrier Free" websites to ensure that people with disabilities have equal to the website.
Pension Payment System: G2C Services in Manipur
The government expenditure towards payment of pension in Manipur constitutes a major component of annual Non-Plan expenditure. The manual system of pension payment suffered from several procedural gaps resulting in forged Pension Payment Order (PPO), impersonation, miscalculation, over payment, non-recovery...
Digital Archiving and Management at National Informatics Centre
Digital objects are being created by governments, private corporations, authors, publishers, librarians, museum curators etc. in the form of text documents, photographs, images, audio and video footage, maps and more. Specifically, the massive volumes of paper generated by government offices can be pulled...
Commercial Tax Computerisation in Uttar Pradesh
The introduction of Commercial Tax Computerisation in UP, has added a new dimension to the department, in dissemination of actual facts related to Commercial taxes at the service of the citizens. It will help the tax department, to effectively monitor the intrastate trade. Traders in Uttar Pradesh will...
Thinking beyond Project Management
The convergence of technology is ushering in a new epoch to render services to the users. A project varies considerably in size, duration and involves a small group of people or large numbers in different parts of the organizations. Project management is a discipline for execution of IT projects. But,...




 Subscribe
Subscribe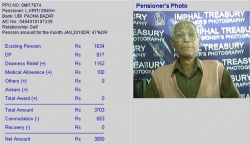



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


