Cyber Governance
Madhya Pradesh: Reaching the un-Reached through ICT
Madhya Pradesh, the second largest State of India having 50 districts & 313 Blocks, is home to a rich cultural heritage and has practically everything; innumerable monuments, large plateau, spectacular mountain ranges, meandering rivers and miles and miles of dense forests offering a unique and exciting...
Upper Siang: Marching Towards ICT Excellence
Upper Siang -a newly created district with its headquarter at Yingkiong in the state of Arunachal Pradesh, encompassing an area of 6188 Sq. km, is a mountainous region endowed with rich natural resources and biodiversity. The mighty Siang River flows though the heart of the district and is referred to...
Fisheries Information System Network (FISHNET)
Kerala is bordered by a range of mountains viz. the Western Ghats on the eastern side and the Arabian Sea on the western side. The coastal line of the Arabian Sea sprawling on the western part of the state is 590 kms in length. The population of fisher folk in Kerala is estimated at about 10.85 lakhs....
Gujarat- Showcasing Irresistible I.T Infrastructure
Gujarat, the westernmost state of country is one of the oldest business points in the world map. It is an abode to some of the largest businesses in the India. A bulk of Gujarat economy is generated from its agricultural and natural resources which includes cotton, sugar, peanuts, groundnuts, various...
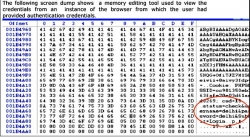
Salted Hashing of Passwords
During the course of Penetration testing of Web Applications at Cyber Security Division, NIC, several security vulnerabilities are identified. One of these vulnerabilities includes the finding that the credentials traveling in clear text can be sniffed from the network. The credentials can also be detected...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


