GIS services
Tirunelveli District - Where District Administration is Reinforced by ICT Tools
Tirunelveli District is one of the oldest districts in Tamil Nadu which is always prominent for its richness in Administration. It is also named Oxford of South India due to its large number of educational institutions. Though the District Administration is always succeeding in a traditional...
Bharat Maps, A Multi-layer GIS Platform
Information Technology, as a cross-cutting frontier of knowledge, has opened several new vistas of applications for daily needs of the civil society. One of them is Geographical Information System GIS technology, which is rapidly becoming a catalyst for several transformational changes in the...
Malnutrition Monitoring System - Fostering the Implementation of ICDS in Malda, West Bengal
The system helps to sort the data based on different key parameters like child growth, MUAC (Mean Upper Arm Circumference) and breastfeeding status, and therefore to identify areas of concern and implement directed intervention. This system has recently upgraded to incorporate detailed information regarding...
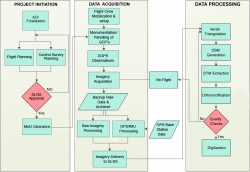
Use of Hybrid Survey Methodology and Bhu-Sarvekshan Software for Resurvey in Bihar
The Bihar state - spread over approx. 94163 sq. Km area, has an administrative setup comprising of 9 divisions, 38 districts, 101 subdivisions, 534 circles and 45,700 mauza(s) i.e. revenue villages. The very first survey of land i.e. Cadastral Survey (CS) of the state was conducted almost a century ago....
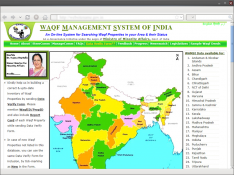
Waqf Management System of India (WAMSI)
Waqf is the permanent dedication by a person professing Islam, of movable or immovable properties for any purpose recognized by the Islamic law as pious, religious or charitable. Waqf Management System of India (WAMSI) is an integrated on-line work flow based Information System for the management...




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


