GIS services
Amravati: Using ICT to Reach the Poor Directly
Amravati is also known as Amrawati or Amraoti. It is believed to be the city of Lord Indra, the king of gods. The city boasts of historical temples of goddess Amba, Lord Shri Krishna and Shri Venkateshwara. But today the district is known for its robust ICT implementations, advanced communication technologies...
Imphal East: e-Governance Deep Rooted with Land Records & CICs
With the computerization of "Land Records" i.e. Loucha Pathap, covering sixty five villages, and the establishment of Community Information Centres (CICs), the district stands apart from others. The computerization effort by the district administration in association with NIC in...
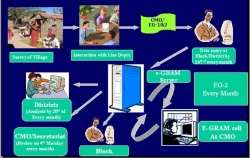
e-Gram in Rajasthan: An ICT Initiative to Transform Rural Governance
Information plays a very crucial role in overall development of the society, and easily accessible information results in a healthy and dynamic democracy. The growing innovations in the use of Information and Communication Technologies have opened up new era of information dissemination. This becomes...
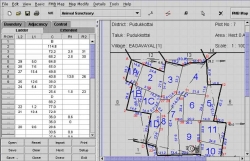
Web GIS for Emergency Plan and Response
Web GIS helps in emergency planning and minimize the damage in case of any eventuality.
Tamilnadu- The Emerging Centre of e-Governance In India
The NIC State Unit of Tamilnadu is not only fostering impeccable ICT activities within the state but also has contributed substantially to growth in the Indian as well as the global ICT industry. With a large pool of highly skilled manpower and a solid backbone of old/new economy Infrastructure, Tamil...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


