Data Centre
DATA LAKE - A Paradigm Shift in the Next Generation Reservoirs
Data lake typically uses low-cost commodity servers in a scale-out architecture where servers can be added as needed to increase processing power and data capacity. In comparison, data warehouse can't be scaled cost-efficiently to process the growing data volume. Data lake provides fast access to...
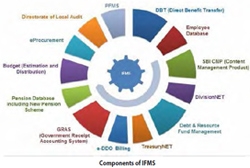
Strengthening Management of Finance In Meghalaya
With the computerization of online treasuries and other related activities using ICT, there has been a paradigm shift in e-Governance of Finance Department of Meghalaya. Most of services are now centralized and hosted at the dedicated servers, where citizen can access over the internet, hazzlefree.
Ensuring Transparency and Reliability in Services provided to Citizens through Efficient ICT Solutions
NIC Punjab has successfully implemented various citizen focussed e-Governance projects in the State fulfilling the objective of making Government services available and accessible 24x7 to the common man at an affordable and hassle-free manner, at the same time ensuring efficiency, transparency...
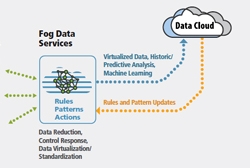
FOG Computing
Fog computing was introduced to meet objectives like improving efficiency and trim the amount of data to be transmitted for processing, analysis and storage, place the data close to the end user and finally provide security and compliance to the data transmission over cloud. Cloud is located up in the...
INFORMATICS- 25 Years of Excellence
An Exclusive Interview with Ms. Neeta Verma, Patron of the Publicationin Publishing on ICT in Government




 Subscribe
Subscribe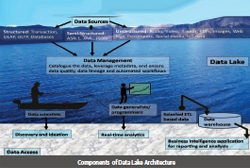



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


