Digitization
AUDIT STATUS MONITORING SYSTEM- A SYSTEM FOR FACILITATING WEB APPLICATION SECURITY AUDIT SERVICES
Strengthening and enhancing the security posture of systems and services is one of the objectives of any organization dealing with information assets of different organizations and departments of Government of India. The Cyber Security Division of NIC is dedicated to this task, having adopted a multi-pronged...
TRANSACTION TERMINALS IN E-GOVERNANCE
Transaction Terminal is a mobile handheld data terminal which has the ability to capture, process and transmit information to host computers in real time. New models of handheld devices come with seamless connectivity options like GSM/GPRS, CDMA and Ethernet. Also, they support all the payment related...
E-COLLECTORATE -A vision shared by Shri D V Swamy, IAS, Collector and DM,Keonjhar
e-Collectorate takes care of the scanning of all communications received by the District Collectorate and then through the inbuilt workflow mechanism traverses to various sections till the files are disposed off. Various file creation for particular application / subject and electronic file movement...
Spatial Information System for the Rajiv Vidya Mission
A Spatial Information System for the 'Rajiv Vidya Mission', covering all the schools of Andhra Pradesh will be very effective in terms of planning and monitoring of the schools for the access, enrollment, retention, quality and monitoring aspects viz., integration of school infrastructure,...
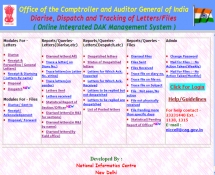
Online DAK Management System: Integrating CAG Office in a Smart Way
The Indian Audit and Accounts Department (IA&AD), 150 years old, with strength of more than 45000 employees in about 211 field offices located all over India and abroad is headed by the Comptroller and Auditor General of India (CAG) Office as the Head of Supreme Audit Institution of India....




 Subscribe
Subscribe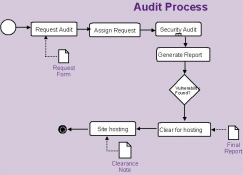




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


