Digitization
TEXTUAL & DEMOGRAPHIC DE-DUPLICATION OF LPG BENEFICIARIES
The subsidized domestic LPG connections in India are almost 14.58 crores. The policy to avail LPG gas connection is -One Kitchen, One Connection with Single bottle or double bottled cylinders for domestic purpose. Textual and Demographic Deduplication (TDD) technique assists in identifying...
GAJAPATI: Using Technology to facilitate e-Governance & Services
The stately district of Gajapati, an erstwhile subdivision of Ganjam district of Odisha, came into being on 2nd October, 1992, is named after the Maharaja Sri Krushna Chandra Gajapati Narayan Deb. The major part of the district is hilly with undulated topography having forest area of approx...
WORK FLOW BASED REGISTRATION OF DOCUMENTS IN MANIPUR
Registration system in Manipur encompasses registration of documents involving changes in ownership and transactions for immovable properties as well as marriage registration with the authority concerned. This system ensures and guarantees legal ownership of title to the party.
e-OFFICE: DIGITAL SIGNING TOOL FOR SECURE DOCUMENTS
Automation has become an integral part any organization through information digitalization leaving away the manual process using physical paper documents. Instead of routing the paper documents manually, the electronic channels have been used extensively for transitioning the documents in digital form....
IMMIGRATION, VISA, FOREIGNERS' REGISTRATION AND TRACKING
The entire IVFRT system envisages the information capture from Visa applicants' details till their exit from India and utilizes these sets of information for intelligence decision making at every stage. This system would facilitate information exchange between MHA, MEA and other agencies such...




 Subscribe
Subscribe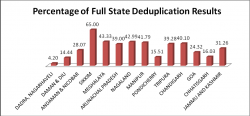





 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


