Digitization
eROR: Register of Ordinary Residents for the Management of Citizen Database
Ordinary Resident Register (ORR) is a physical register maintained in the state of Tripura, at the lowest tier of local self-government (urban as well as rural), to record the details of the citizens. Citizens are not entitled to civic services and benefits, unless their names are recorded...
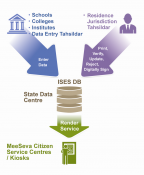
ISES- Integrated Socio-Economic Survey of Students
The Government of Andhra Pradesh has desired to deliver the citizen-centric services from a centralized location through all citizen service centres such as e- Seva, AP Online, CSCs across the state under a new initiative called MeeSeva. A web based application- ISES has been designed and developed...
Empowering People Participation in Decentralized Planning Process through INTEGRATED SPIDER & e-MANCHITRA GEO PORTALS
To overcome the maladies affecting the manual system and to reduce the workload and to increase the efficiency, transparency, visualization; SPIDER & e- MANCHITRA portals have been developed and integrated. The integration of SPIDER & e-MANCHITRA Geo portals has made information visualization easier,...
The Importance of Standards and its Use in Healthcare
Traditionally, the healthcare environment consisted of a set of loosely-connected, organizationallyindependent units. Health-IT standards provide the foundation for institutional data sharing with disparate healthcare systems and integration of this clinical data with diagnostic equipment such...
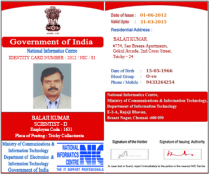
IDENTITY CARD MANAGEMENT SYSTEM (ICMS)
Identity Card Management System (ICMS) is a fully integrated system that identifies individuals of an organization by way of issuing Identity Cards (ID Cards). It assists in controlling access to the resources of an organization on the basis of such ID Cards. The new system provides...




 Subscribe
Subscribe


 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


