Digitization
REST vs. Messaging for Microservices Discover how to choose the right communication style for Microservices
Two common protocols used in microservices are HTTP request/response with resource APIs and lightweight asynchronous messaging when communicating updates across several microservices. This way the small, lightweight modules in MSA architecture can achieve the business domain process. MSA is the established...
eGramSwaraj Simplified Work-based Accounting application for Panchayati Raj
eGramSwaraj has improved the functioning of Panchayati Raj Institutions, providing citizens with a platform to connect with local representatives and participate in local governance. It has enabled greater transparency and accountability in the functioning of the Panchayats, which has been essential...
NICler Reimagining Education through Technology
NICler is an innovative assessment tool that has been designed to gamify learning and promote adaptive learning. This highly cost-effective tool is being widely adopted in over 30,000 schools across Chhattisgarh, and has proven to be a valuable addition to the education system. It has increased student...
Double Diamond Design Process An Advanced Framework for a Successful UX Design
Double Diamond Design Process involves understanding user needs by exploring and gathering information, collaborating with different disciplines to uncover challenges and opportunities, and refining the core problem. The design approach allows to generates multiple ideas, improves them through feedback...
Puri, Odisha Setting a benchmark in delivering ICT Solutions to foster excellence
NIC Puri District Centre has established itself as a state-of-theart ICT service provider to various departments and stakeholders under the District Administration for enabling transparent, efficient, and reliable Government to Citizen services. It is specially engaged in the development of a variety...




 Subscribe
Subscribe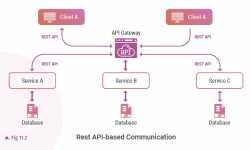




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


