Digitization
PM Poshan Shakti Nirman Portal Enhancing Efficiency and Transparency in School Nutrition Programs
MP State PM Poshan Shakti Nirman Portal enhances the Pradhan Mantri Poshan Shakti Nirman scheme by automating food grain provisioning, ensuring transparency with Aadhaar-enabled authentication, and facilitating timely digital payments. This digital platform streamlines operations to deliver...
Cryptographic Key Management Balancing Security and Usability in Key Management
The article explores three cryptographic key management approaches: storing keys in application servers, using Hardware Security Modules (HSMs), and implementing software-based HSMs on dedicated servers and isolated VLANs. It assesses each method security, cost- effectiveness, and practicality. While...
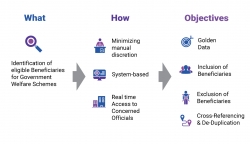
Unified Data Hub Empowering Proactive Governance through Integrated Solutions
UDH has established an adaptable system for validating and eliminating duplicate beneficiaries. Presently, it encompasses Puducherry residents and their enrolled schemes, incorporating 24 departments and 150 central and state schemes. Its scalability allows seamless integration with new schemes. The...
Khowai, Tripura Transformative IT Initiatives Shaping the District Future
Since its inception, NIC Khowai District Centre has been a crucial force in providing technical support and fostering skill development among diverse stakeholders. Leveraging its ICT expertise, NIC Khowai efficiently implements numerous National and State-level ICT projects with transparency. The centre...
iHRMS Punjab Tool for Effective HR Management & Decision Support
iHRMS Punjab is a unified HRM platform that encompasses all government entities in Punjab. It simplifies and standardizes HR processes from employee onboarding to offboarding, ensuring efficiency. With role-based workflows, it enables stakeholders to carry out tasks seamlessly. Over six years, Punjab...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


