Digitization
Parbhani, Maharashtra Round the clock ICT support during COVID-19 Pandemic
Besides the regular technical and infra support for implementing various State and Central eGovernance Projects at grass root level, the NIC Parbhani District Centre has been instrumental in enabling ease of access to the public services provided by the various government departments...
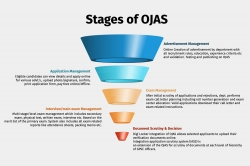
OJAS (Online Job Application System) - A complete solution for speedy and transparent recruitment process of Government
Since inception in 2009, more than 100 departments have been using OJAS platform for their recruitments of various class I, II & III posts. Over 2000 exams have already been conducted using the portal. In 2014, the system was made compulsory by the Government of Gujarat for any type of recruitment....
Uttarakhand Teachers Eligibility Test (UTET) Online - Exam Management System-2019
Till 2018, the entire process UTET was carried out manually by the Uttarakhand School Education Board. Understanding the complications and challenges of the manual system, NIC- Uttarakhand proposed Department of School Education, Uttarakhand to design and develop a computerized system enabling automation...
KARNATAKA The Silicon Valley of India pioneers in e-Governance with ICT excellence
Karnataka is the eighth largest state of India and is located in the country's south western region. Formed on 1st November 1956, the state was earlier known as the State of Mysore, and was renamed Karnataka in 1973. Being a home to sculptured temples, hill ranges, beaches and other beautiful...
District HOOGHLY, West Bengal Channelising e-Governance through advanced ICT techniques
Hooghly, with its headquarters located at Chinsurah town, lies within the Burdwan division of the state of West Bengal. History suggests the name Hooghly is derived probably from the word 'Hogla', a tall tree, which grows in abundance on the river banks and in the marshy low lands below...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


