Police
JHARSUGUDA: Revolutionizing Governance through ICT
Jharsuguda - one of the most industrially developed districts in the state of Odisha, is situated at a distance of 372 km from the state capital Bhubaneswar. It was created on 1st April, 1994 bifurcating Sambalpur district. It covers an area of 2, 081 sq. km. and lies between 21.82 degree north...
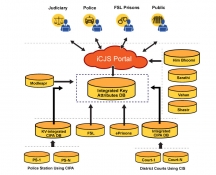
iCJS: Inter-operable Criminal Justice System
The Interoperable Criminal Justice System (iCJS) has been developed for the process of speedy justice by facilitating data-exchange between the courts, police/prosecution, jails and the forensic labs. The application has been developed by NIC for the District courts, prisons and Police...
MedLEaPRFIRST STEP TOWARDS ICT ENABLED INTEGRATED JUSTICE DELIVERY SYSTEM
Medico Legal Examination and Postmortem Reports System (MedLEaPR) is a generic software developed by NICHaryana to facilitate computerization of MLRs & PMRs. Further, the system is workflow based, which provides requisite access security, based on roles & responsibilities...
SMS Application Development using Open Source
SMS - Short Messaging Service has changed the life of the common man, leave alone the benefits of a mobile phone, in staying connected and doing transactions while on the move. SMS integration with e-Governance applications has taken a big leap in reaching the masses renaming SMS as Smart Management...
ICT Initiatives in HP Police
Sh. G S Gill, IPS & Director General, Himachal Pradesh Police speaks to Informatics on the various e-Governance Initiatives undertaken successfully in the HP Police Department.




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


