Police
Nabarangpur, Odisha Empowering governance for the last-mile service seeker
Established in 1997, NIC Nabarangpur is a pivotal ICT service provider for Divisional and District administration, excelling in G2G and G2C services. Renowned for executing state and central government e-Governance projects, the centre has played a vital role in the digital transformation of the...
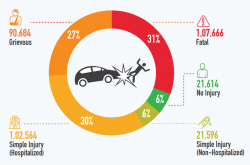
iRAD Making Better and Safer Road Ecosystems
iRAD Road Accidents have become a menace in India. iRAD tries to solve it by creating an integrated road accident database to help authorities to take proactive decisions and make Better and Safe Roads for All.
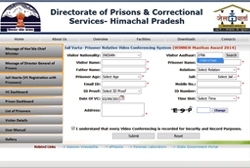
JailVaarta: Innovative software to facilitate Video Conferencing of Prisoners with Relatives
JailVaarta is an innovative application developed by NIC, for primarily facilitating the prison inmates and their relatives to interact conveniently without the relatives visiting prison.
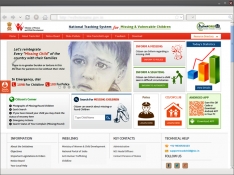
TrackChild2.0 : National Tracking System for Missing and Vulnerable Children
The portal TrackChild 2.0 - National Tracking System for Missing and Vulnerable Children (www.trackthemissingchild.gov. in) is dedicated to the cause of tracking missing and vulnerable children. It holds the national database of children who are reported as missing or found along with those...
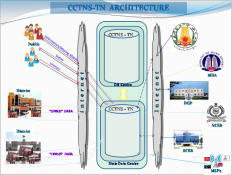
Implementation of CCTNS Project in Tamil Nadu
The ambitious Crime and Criminals Tracking Network & System (CCTNS) project was conceived as one of the 31 Mission Mode Projects of Indias National e-Governance Plan (NeGP) for transforming Police into an IT-based force and to improve the delivery of citizen-centric services. The project...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)


