G2C
Pension Payment System: G2C Services in Manipur
The government expenditure towards payment of pension in Manipur constitutes a major component of annual Non-Plan expenditure. The manual system of pension payment suffered from several procedural gaps resulting in forged Pension Payment Order (PPO), impersonation, miscalculation, over payment, non-recovery...
Arunachal Pradesh: Initiating e-Governance Projects in Major Sectors
Stretching from snow-capped mountains in the north to the plains of the Brahmaputra valley in the south, endowed with vast forest cover, home to large number of fauna and flora, Arunachal Pradesh - the Land of Rising Sun has enough potential to become famous worldwide for eco-tourism. Itanagar the capital...
Muzaffarpur: A Major Hub for e-Governance in North Bihar
Muzaffarpur, a major town of north Bihar, situated on the Indo-Gangetic plain, has earned international encomiums for its delicious Shahi Litchi which are exported to other parts of the country and even abroad. Muzaffarpur has innumerable historical sites and monuments. There are a lot of Buddhist Viharas...
KERALA: ICT in the land of Backwaters
Kerala "Gods Own Country", is the first Indian State to achieve total literacy. NIC Kerala was established in 1987 as part of nationwide computer and communication network, NICNET. NIC district centers are located in the 14 district head quarters attached to the collectorate.
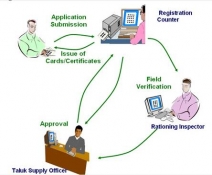
ICT an enabler for an efficient Public Distribution System in Kerala
Public Distribution of Food grains has always been an integral part of any State overall food policy. It has been evolved to reach the urban as well as the rural population in order to protect the consumers from the fluctuating and escalating price syndrome. TETRAPDS (Targeted Efficient Transparent Rationing...




 Subscribe
Subscribe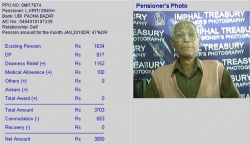




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


