G2C
e-Hospital@NIC: Simplifying Health Care Delivery
Tucked away at the southernmost tip of the Northeast, the state of Tripura has made significant contribution to public health care by pioneering e-Hospital@NIC-an integrated Hospital Management Information System (HMIS) which now runs in almost 30 major public hospitals across the country,...
COMBATING MALNUTRITION & UNDER-5 MORTALITY IN NAGAON DISTRICT OF ASSAM THROUGH ICT
Launched on October 2, 1975, the Integrated Child Development Service (ICDS) Scheme today represents one of the worlds largest and most unique programmes for early childhood development. In the case of Nagaon District, the mortality rate of children below 5 years has been higher than the average...
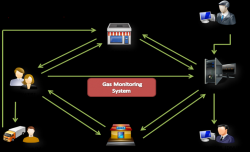
EASYGAS, KISAN: Citizen-Centric IT Innovations from Gonda, Uttar Pradesh
Achieving milestone is not an everyday business. Claiming appreciation for achievement is even tougher. The feeling goes beyond the expected elation, when endeavour, designed and perspired for common good catches peoples eyes to attain recognition. Project EASYGAS and project KISAN, the two...
CSI-NIHILENT E-GOVERNANCE AWARDS 2012-13
.CSI Nihilent e-Governance Awards have been instituted to acknowledge the exemplary initiatives/projects/services in the realm of e-Governance. Running into its second decade, the award is a golden yardstick for evaluating the mileage of various e-Governance initiatives running in the country. Alike previous...
Publishing of Exam Results & Online Counselling from NIC Data Centre T
NIC Data Centre, Delhi has always played a proactive and pivotal role in providing robust, reliable and secure service-delivery platform to its hosted applications, be it a website, portal or any e-Governance project. Continuing with its decade long success trail, this year too, NIC Data Centre...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


