G2C
ISES- Integrated Socio-Economic Survey of Students
The Government of Andhra Pradesh has desired to deliver the citizen-centric services from a centralized location through all citizen service centres such as e- Seva, AP Online, CSCs across the state under a new initiative called MeeSeva. A web based application- ISES has been designed and developed...
SAMAY SUDHINI SEVA- Online Monitoring of Time Bound Services
UT Administration of Daman & Diu and Dadra & Nagar Haveli in collaboration with National Informatics Centre have implemented an online web based Monitoring System for time bound services known as Samay Sudhini Seva.
LAKSHADWEEP ISLANDS- Digitally Bridging the Nautical Seclusion
The Union Territory of Lakshadweep (UTL) is geographically dispersed in the Arabian Sea with its capital at Kavaratti. It has achieved enormous success in deliverance of ICT services to its citizens despite its geographical isolation and bandwidth insufficiency, using the reliable and efficient infrastructure,...
RAJASTHAN- Celebrating Twenty Five Glorious Years
NIC Rajasthan is celebrating silver jubilee of its establishment this year. The celebrations have started and the long journey with ups and downs has been quite fruitful. Today with the efforts of team NIC, the state of Rajasthan is surging ahead as a leader in e-Governance and ICT development,...
SEHORE: Heralding a Paradigm Shift in e-Governance Regime
Sehore lies in the foothills of Vindhyachal Range surrounded by of Malwa region in Madhya Pradesh. It is about 39 Kms away from the state capital Bhopal towards south and spread across 6578 Sq. Kms. Shaiva, Shakta, Jain, Vaishnav, Budhists and Nath priests made Sehore a significant seat of their...




 Subscribe
Subscribe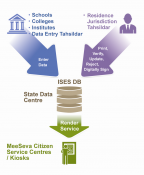





 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


