G2C
OSMANABAD District:- Pioneering in implementing e-Governance projects, products and initiatives
Some of the prominent ICT activities in line with the Digital India Initiative in Osmanabad are development and implementation of Cashless Osmanabad Mobile App, Online e-Blood Bank project, Aadhaar at Birth concept, designing NETSTAT NICNET monitoring tools and WEBSTAT contents uploading management.
Soil Health Card
Soil Health Card provide soil nutrient status of a farmers holding and advise him on the dosage of fertilizers and need for soil amendments for a healthy soil in the long run. The Government plans to issue Soil Health Cards to 14 crore farmers in a cycle of 2 years.
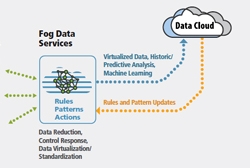
FOG Computing
Fog computing was introduced to meet objectives like improving efficiency and trim the amount of data to be transmitted for processing, analysis and storage, place the data close to the end user and finally provide security and compliance to the data transmission over cloud. Cloud is located up in the...
Bihar State ICT Initiatives:Soaring High With Excellence In m-Governance
NIC Bihar has been identified as a Mobile Competency Centre and has been involved with the design and development of several key Apps for various departments at a variety of levels of administration.
Union Minister Inaugurates Digital Government Research Centre (DGRC) in Patna
DGRC is a centre of excellence which strives to nurture, visualize and implement ideas in the field of eGovernance research and innovation




 Subscribe
Subscribe



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


