G2C
Nabarangpur, Odisha Empowering governance for the last-mile service seeker
Established in 1997, NIC Nabarangpur is a pivotal ICT service provider for Divisional and District administration, excelling in G2G and G2C services. Renowned for executing state and central government e-Governance projects, the centre has played a vital role in the digital transformation of the...
Mobile App Development - Technologies/ Frameworks and Steps to Develop Mobile App
Today, the focus area in eGovernance, to cover larger user base, is through Mobile Apps because of the availability of smart phones with majority population in India and extensive mobile connectivity. A forecast of smartphone users in India in 2021 is 76 crores which will make more than...
Load Testing as a Service - Self Service model for application load testing
Modern day G2C services expect very high concurrency in production. In order to ensure that the quality of service matches the expectations of end user, it is vital to perform a thorough load testing of application prior to its release. Load testing of such application requires considerable investment...
Tirunelveli District - Where District Administration is Reinforced by ICT Tools
Tirunelveli District is one of the oldest districts in Tamil Nadu which is always prominent for its richness in Administration. It is also named Oxford of South India due to its large number of educational institutions. Though the District Administration is always succeeding in a traditional...
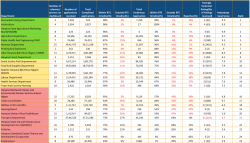
Antyodaya SARAL Haryana: A unified platform ensuring hassle-free & time-bound delivery and tracking of G2C services in the State
Having implemented Antyodaya SARAL, Haryana is the first state in the country to integrate so many schemes and services on one platform. The powerful solution developed by NIC Haryana has channelized the process of bringing about a fundamental behavioral change in the way the government functions, and...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


