G2C
Workshop on Open Government Data & Civic Engagement
With the goal to discuss the important aspects of Open Government Data & Civic Engagement, National Informatics Centre (NIC) conducted a workshop on April 4, 2013 at India Habitat Centre, New Delhi. Though primarily the workshop was targeted at Data Controllers nominated by various Ministries/...
ELECTRICITY DEPARTMENT, DADRA AND NAGAR HAVELI
Electricity Department functions as an integral part of the administration of Union Territory of Dadra & Nagar Haveli. The organization runs under the aegis of Secretary (Power) and its day to day work is handled by the Executive Engineer (Elect.) at Division level. The website has...
ELECTRICITY DEPARTMENT, DADRA AND NAGAR HAVELI
Electricity Department functions as an integral part of the administration of Union Territory of Dadra & Nagar Haveli. The organization runs under the aegis of Secretary (Power) and its day to day work is handled by the Executive Engineer (Elect.) at Division level. The website has...
Inauguration of Single Window Kiosk at Tehsils in Hardoi, Uttar Pradesh for issuance of Certificates.
District Magistrate, Hardoi Shri A.K Dwivedi inaugurated the single window kiosk at tehsil Sadar on 1st April 2013. Computerized Caste, Income and Domicile Certificates will be issued to the citizens from these Kiosks. The computerized certificate delivery system has multiple benefits over the...
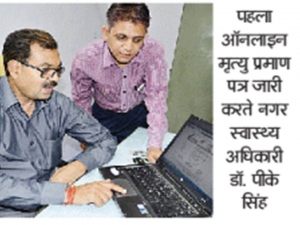
Digitally Signed Birth & Death Certificates becomes a reality in Lucknow, Uttar Pradesh
Days have gone when people had to make multiple visits to the municipal corporation offices for applying and receiving birth or death certificates. Lots of time & money had to be spent by the citizens for obtaining these government services. However, the scenario changed in the state with the...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


