Articles
Solan: ICT in the Mushroom City of India
Solan, located 46 kilometres south of Shimla, is gateway to Himachal and is named after the Hindu goddess Shoolini Devi. It is popularly known as the Mushroom City of India, because of the vast mushroom farming in the area and the City of Red Gold, for being the bulk producer of tomatoes.
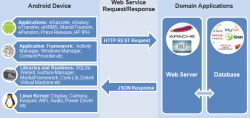
Android Mobile Apps to Supplement Web Content
India has the fastest growing telecom network in the world credited to its high population and development potential. The total number of telephones in the country stands at 957.61 million, while the overall teledensity has increased to 76.75% as of 30th September 2014. The total number of mobile...
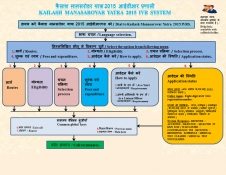
IVRS@NIC: Kailash Mansarovar Yatra (KMY) 2015
NIC TDPP division IVRS has been an integral part of the telephony revolution that the country has witnessed since the last decade. Right from the challenging period of analog cards and C++ codes interacting with card API for creating a call flow in the late 90s, the IVRS evolved to GUI Call-flow Management....
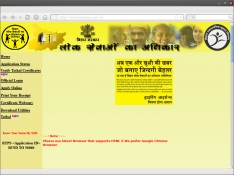
Empowering Citizens through e-Services & m-Governance
IT has been on the top of the agenda of the State Government. e-Governance in Bihar has helped in increasing transparency and accountability in the government functioning. This is an exclusive Interview with Dr. S. Siddharth, Secretary, Department of IT and Department of Labor, Govt. of Bihar...
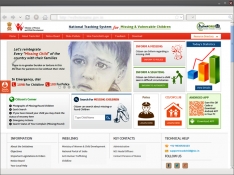
TrackChild2.0 : National Tracking System for Missing and Vulnerable Children
The portal TrackChild 2.0 - National Tracking System for Missing and Vulnerable Children (www.trackthemissingchild.gov. in) is dedicated to the cause of tracking missing and vulnerable children. It holds the national database of children who are reported as missing or found along with those...




 Subscribe
Subscribe

 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)


