Articles
Implementation of Aadhar based Public Distribution System in Jharkhand
The Food, Civil Supplies & Consumer Affairs Department, Govt. of Jharkhand decided to develop Aadhar based, web enabled - Public Distribution System (PDS) using Hand held Terminals (HHT) at the 23614 Fair Price Shops (FPS) in the state. This enables end-to-end use of ICT ranging...
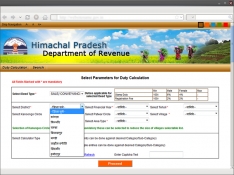
Himachal Integrated Registration Information System (HIMRIS)
Registration of deeds is the first and the most critical step in acquiring title to land or property and thus, assumes significance for those who are involved in these transactions. The registration of these transactions is mandatory to make them legal, otherwise ownership rights cannot be claimed/transferred....
Uploading of Court Cases Data in NJDG & SMS Services under e-Courts in Manipur
Under the e-Courts project, all the 32 courts of Manipur located at 13 different courts complexes have started using the Case Information System (CIS) software to record the daily court proceedings. The National Judicial Data Grid (NJDG) is a part of the ongoing e-Courts Integrated Mission...
PEARL Suite: Property Registration for Government of Kerala
As part of e-governance, to carry out all the activities of Sub Registrar offices in Kerala, Windows based client-server application PEARL was initiated in the year 2000 and was implemented in all the 311 offices in Kerala. Even though the system automated the activities of SRO, the decentralized data...
Success Story of eOffice in the Greater Hyderabad Municipal Corporation (GHMC), Telangana
The Greater Hyderabad Municipal Corporation (GHMC), Hyderabad under the Govt. of Telangana is a huge organization with administrative jurisdiction of over 625 Sq Kms and with a mandate to cater to the day-to- day civic needs of about 90 lakh population. It has 5 Zonal Offices and 18 Circle Offices....




 Subscribe
Subscribe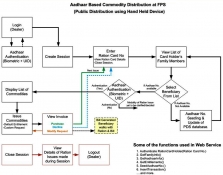



 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


