Articles
Strengthening Management of Finance In Meghalaya
With the computerization of online treasuries and other related activities using ICT, there has been a paradigm shift in e-Governance of Finance Department of Meghalaya. Most of services are now centralized and hosted at the dedicated servers, where citizen can access over the internet, hazzlefree.
Aadhaar Authentication Platform
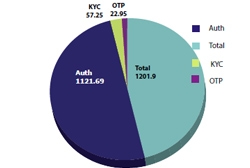
The Authentication Services is integrated with 110 plus applications of States & Central Government Departments and Ministry with the monthly transaction of around 12 Crores in the month of November 2017. Indian Army, Public Distribution System, Digital Locker, CBSE, Jeevan Pramaan, Biometric...
Civil Secretariat Goes Wireless
With its Wi-Fi implementation, the Arunachal Pradesh Civil Secretariat becomes first of its kind in the Country to go wireless. Covering the entire Secretariat which consists of four blocks, this set-up has been designed for wireless access of a large number of users to the tune of about 6500 concurrent...
FOG Computing
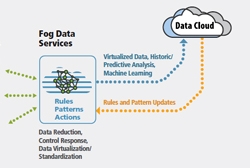
Fog computing was introduced to meet objectives like improving efficiency and trim the amount of data to be transmitted for processing, analysis and storage, place the data close to the end user and finally provide security and compliance to the data transmission over cloud. Cloud is located up in the...
Kendriya Vidyalaya Shaala Darpan
Kendriya Vidyalaya Shaala Darpan platform has been implemented by NICSI on NIC Clouds for 1185 Kendriya Vidyalayas across the country. A mammoth task was accomplished online in one of the largest school systems in the world with an estimated 1.2 million students and 50,000 teachers.




 Subscribe
Subscribe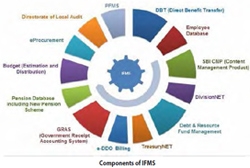



 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


