Articles
Paschim Bardhaman The Industrial Hub of West Bengal
NIC Paschim Bardhaman, the technological backbone of the district administration, drives digital transformation through innovative e-Governance solutions. From developing the district website and mobile application to implementing e-Office, iRAD, and Election Manpower Management Systems, NIC...
Hanumangarh, Rajasthan Digital transformation through advanced ICT solutions
NIC Hanumangarh has been instrumental in driving e-Governance initiatives and fostering a technology-driven administrative ecosystem. The centre facilitates seamless G2C and G2G services, enhancing governance efficiency. The district unit provides essential digital resources, supporting initiatives...
Durg, Chhattisgarh Accelerating e-Governance with ICT-Driven Innovation
NIC Durg District Centre drives the Digital India movement by seamlessly integrating technology into governance. Committed to transparency, efficiency, and citizen empowerment, it implements e-Governance initiatives at all levels. Through ICT-driven solutions, NIC Durg bridges the digital divide...
Uttarakhand Bridging Tradition and Technology in the Land of Gods
Uttarakhand, the Land of Gods, is embracing digital transformation, leveraging ICT to enhance governance, transparency, and citizen services. Since 2001, NIC Uttarakhand has been the State technology backbone, developing e-Governance solutions, secure infrastructure, and data-driven frameworks. Aligning...
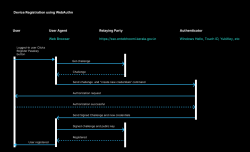
Passkeys and WebAuthn Revolutionizing Authentication with the Passwordless Technology
Passkeys and WebAuthn are revolutionizing digital authentication by eliminating passwords and enhancing security. WebAuthn, a FIDO2 standard, uses pub- lic key cryptography for secure authentication, storing private keys on devices and preventing phishing and credential theft. In Kerala Entebhoomi...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


