Articles
Karaikal, Puducherry Building Digital Systems for Transparency, Accountability in Governance
NIC Karaikal, with support from NIC State and Central teams, empowers the District Administration through Open Data platforms, real-time dashboards, citizen-centric portals, mobile apps, and social media integration. It ensures transparency with accessible datasets, real-time tracking of projects, and...
Hyderabad Urban Telangana Rising Hyderabad in e-Governance
NIC Hyderabad initiatives aim to create a digital ecosystem where opportunities abound for individuals and institutions alike. For citizens, this means improved access to essential services, simplified processes, and real-time grievance redressal. For the government, it translates to enhanced efficiency,...
Meghalaya State Empowering Governance, Enabling Growth
NIC Meghalaya has been a cornerstone in driving digital innovation and e-Governance across the state, bridging gaps between technology and public service delivery. Through initiatives like e-District, e-Prisons, and Meghalaya Sign Bank, it has revolutionized access to services, enhanced transparency,...
Jammu and Kashmir Jammu Heritage, Kashmir Splendor: Driven by Technology
Jammu and Kashmir, India northernmost Union Territory, blends cultural richness with technological progress. Since its restructuring in 2019, NIC J&K UT Centre has driven digital transformation, offering over 330 e-Services across key sectors like healthcare and educa- tion. Milestones include...
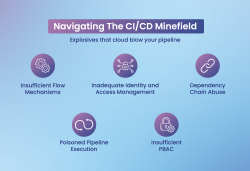
Securing CI/CD Pipelines Addressing the Unique Challenges in DevOps
CI/CD pipelines enable fast software delivery but come with security risks like weak flow control, IAM gaps, and dependency exploits. Mitigation includes role-based access control, multi-factor authentication, secure secrets management, and automated testing. Tools like Jenkins and GitLab CI/CD...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


