Articles
eCabinet - Automate Cabinet meetings in paper free and virtual mode
eCabinet/ eMantrimandal is a powerful software portal for State governments to conduct Cabinet meetings electronically and online mode. Developed by NIC, it maximizes usage of technology in meetings and reduces paper use. eCabinet automates work flow activities of meetings; before, during and after....
eAbgari - End-to-End Solution for Comprehensive Transformation of State Excise
eAbgari has been the single most transformational factor in state excise sector and has greatly increased the department's enforcement and regulatory capabilities through ICT driven process reengineering. Seamlessly integrating a wide array of innovative technologies - the web, QR codes,...
Khargone District - Citizen Centricity is the way forward for eGovernance
Known for its hot weather conditions, Khargone is an emerging hub of Chili and Cotton production in Madhya Pradesh. The district mostly irrigated by the waters of River Narmada, has Satpuda Hill range that borders with Maharashtra. By developing need based timely IT solutions NIC Khargone is...
Kamareddy District - Committed Towards Digital Governance
NIC, Kamareddy District Centre is located in the premises of Collectorate, for providing ICT support and implementation of eGovernance Projects in the district and to provide the NICNET services for data transmission from District to various Departments. NIC District Centre has spearheaded the...
Changlang District - The ICT initiatives in The Land of Bio-diversity
During Covid-19 pandemic period ICT services of the National Informatics Centre Changlang District Centre became all the more important. The District Centre in collaboration with the State Centre implemented various services, which facilitated emergency movement of people and goods. Support...




 Subscribe
Subscribe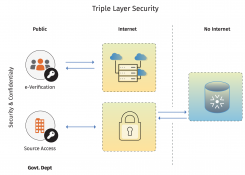




 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

