Articles
Andhra Pradesh State - Building the State through digital eGovernance
The State of Andhra Pradesh has made significant contributions in various sectors over the decades. With the advent of Information Technology Age, the State has started making good use of the Technology in more efficient running of the Administration and in the implementation of various Government...
The Digital India Awards 2020 ceremony
The Digital India Awards 2020 ceremony (sixth edition) took place virtually on 30th December, 2020 and the awards were conferred by the Hon'ble President of India, Shri Ram Nath Kovind from Rashtrapati Bhawan via video conferencing (VC), in the presence of Hon'ble Union Minister of Law...
COVID-19 e-Pass - A ServicePlus Success Story
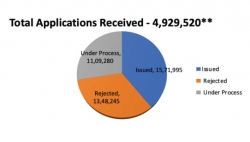
The Covid-19 menace was spreading vigorously in the country. On 24th March 2020, honourable Prime Minister of India declared a nationwide lockdown for three weeks. It was part of a preventive measure to tackle the pandemic. Lockdown limited the movement of the entire population of the country, but...
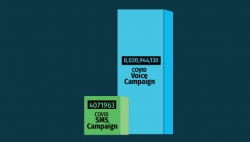
Messaging Services of NIC
During COVID pandemic, SMS service has seen a growth of almost 24% and has played a critical role in communicating with citizens
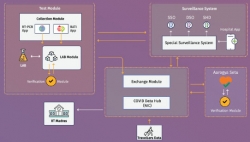
Integrated Core COVID-19 Management Framework - Ensuring availability of data across systems for better management of COVID-19 crisis
Corona virus pandemic has spread across the world at a fast pace disrupting life in unprecedented ways. Government of India has taken multiple measures like nation-wide lockdown, identification of hotspots/ containment zones, isolating patients and suspects, contact tracing, surveillance besides...




 Subscribe
Subscribe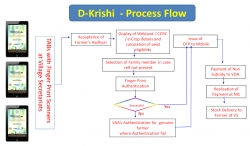


 Flipbook
Flipbook PDF (5.0 MB)
PDF (5.0 MB)

