Articles
INTERNETING IN THE FUTURE - WEB 3.0
Internet started as a military exercise to link offices across the USA, has become ubiquitous in every sphere of human lives whether living in rural, urban or semi-urban habitats. The information flow from top to bottom and vice-versa has made the people more knowledgeable not only about their rights...
OPEN SCHOOLING SYSTEM THAT TOUCHES & CHANGES THE LIVES OF MILLIONS
The National Institute of Open Schooling (NIOS), formerly known as National Open School (NOS), was established in November, 1989 as an autonomous organisation in pursuance of National Policy on Education, 1986 by the Ministry of Human Resource Development (MHRD), Government of India. NIOS is mandated...
KERALA : E-SERVICES FOR "GOD'S OWN COUNTRY"
Kerala, popularly known as "God's Own Country", has had far reaching achievements in providing a better quality of life to its citizens. With a very high Human Development Index (UN Indicator), in par with most western countries, UN has declared "Kerala Model" as one to emulate...
CHHATTISGARH - State on a Mission with a Vision
Located at the centre towards east of India, the country's 13.79 million hectare "Rice Bowl" came into existence on 1st November 2000 and soon it paved the path towards all round development. Having gifted with eye catching scenic beauty, the numerous waterfalls, rivers, caves vast forests...
PRIME MINISTER'S MEDIA CORNER: OFFICIAL MEDIA RESOURCES FROM PM'S OFFICE ANYTIME ANYWHERE!
The Prime Minister's Media Adviser, Shri. Pankaj Pachauri along with his team felt the need of the news media houses to have access to quality-rich authentic and current media resources pertaining to the Prime minister. It was felt that resources such as Photos and Videos would enable the news...




 Subscribe
Subscribe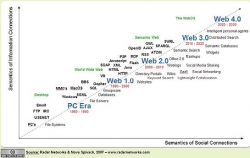





 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


