Articles
ALFA - AUTOMATION OF LOCAL FUND AUDIT: BRINGING TRANSPARENCY IN INTERNAL AUDIT
The Automation of Local Fund Audit (ALFA) is to provide more fiscal discipline and efficiency in audit process. The launch of ALFA has brought in a more transparent, efficient and accurate Audit Process along with basic citizen services.
WEB RATNA AWARDS: PROMOTING EXEMPLARY INITIATIVES IN E-GOVERNANCE
Enthusiasm marked the second season of the Web Ratna Awards. It was held on 10th December, 2012 at Dr. D.S Kothari Auditorium, DRDO Bhawan, Dalhousie Road, New Delhi. Hon'ble Minister of Communications and Information Technology, Shri Kapil Sibal felicitated the winners. Hon'ble Ministers...
E-COLLECTORATE -A vision shared by Shri D V Swamy, IAS, Collector and DM,Keonjhar
e-Collectorate takes care of the scanning of all communications received by the District Collectorate and then through the inbuilt workflow mechanism traverses to various sections till the files are disposed off. Various file creation for particular application / subject and electronic file movement...
TRANSACTION TERMINALS IN E-GOVERNANCE
Transaction Terminal is a mobile handheld data terminal which has the ability to capture, process and transmit information to host computers in real time. New models of handheld devices come with seamless connectivity options like GSM/GPRS, CDMA and Ethernet. Also, they support all the payment related...
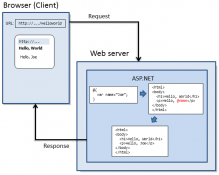
WEB PAGES WITH RAZOR SCRIPTING NEW VIEW ENGINE IN ASP.NET
Razor syntax is based on technology from Microsoft called ASP.NET, which in turn is based on Microsoft .NET Framework. The Razor syntax gives you all power of ASP.NET, but using a simplified syntax that's easier to learn and it can be used with existing ASP.NET Web Site.




 Subscribe
Subscribe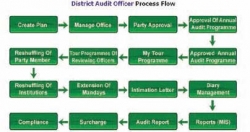




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


