Articles
Odisha State Endeavouring Digital Transformation for Effective Governance
In the ever-evolving landscape of technology, NIC Odisha consistently stood at the forefront, driving digital transformation and fostering innovation. Known for organizational trustworthiness and cost effective solutions at both State level and Pan India, NIC Odisha thrives on applications...
Haryana State Empowering Haryana Through Digital Innovation
NIC Haryana has transformed the State into a digitally empowered economy by implementing innovative, cashless, paperless, and faceless solutions. These efforts ensure fast, hassle-free, and time-bound service delivery while combating nepotism and corruption. Flagship programs like Antyodaya SARAL, Parivar...
Securing Machine Identities with Multi-Factor Authentication Enhancing Security and Compliance in a Perimeter-less Network Era
Multi-Factor Authentication (MFA) for machine identities adds an extra layer of security by requiring multiple verification methods during authentication. This helps protect against cyber threats by ensuring that only authorized machines can access systems and data. Implementing MFA for machine...
Cryptographic Key Management Balancing Security and Usability in Key Management
The article explores three cryptographic key management approaches: storing keys in application servers, using Hardware Security Modules (HSMs), and implementing software-based HSMs on dedicated servers and isolated VLANs. It assesses each method security, cost- effectiveness, and practicality. While...
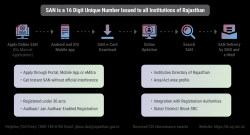
Sanstha Aadhaar Streamlining Institutional Registration and Monitoring
Sanstha Aadhaar integrates Sanstha Aadhaar Numbers across Rajasthan to monitor economic activities, supporting Economic Census and NSSO Surveys for informed policy- making. It ensures transparency and efficiency through online registration, certification issuance, and integration with state...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.6 MB)
PDF (4.6 MB)


