News
GIS SESSION AT LBSNAA, MUSSOORIE
A session on Geographic Information System (GIS) Technology had been delivered at Lal Bahadur Shastri National Academy of Administration, Mussoorie by Dr. Vandana Sharma, Head, Remote Sensing and GIS Division, and Deputy Director General, National Informatics Centre, New Delhi on 14th July...
Muzaffarnagar, 20 November 2010 - Mr Sachin Pilot, Min of State, Comm & IT inaugurated 5 Post Offices through NIC Video Link
Inauguration of Post offices by Mr. Sachin Pilot, Union Minister of State for Communication and Information Technology – Muzaffarnagar (UP) Through NIC Video link Union Minister of State for Communication and Information Technology Sachin Pilot on 20th November 2010 dedicated 5 post offices...
Implementation of eFile in NIC Nagaland
Along with rest of the state in the country, a demo on e-File application under eOffice was organized at NIC Nagaland State Centre, Kohima on 04 November 2010. The DIOs and DIAs of the NIC Nagaland District Centres also participated through video-conferencing. Mr. Kezungulo Medikhru,...
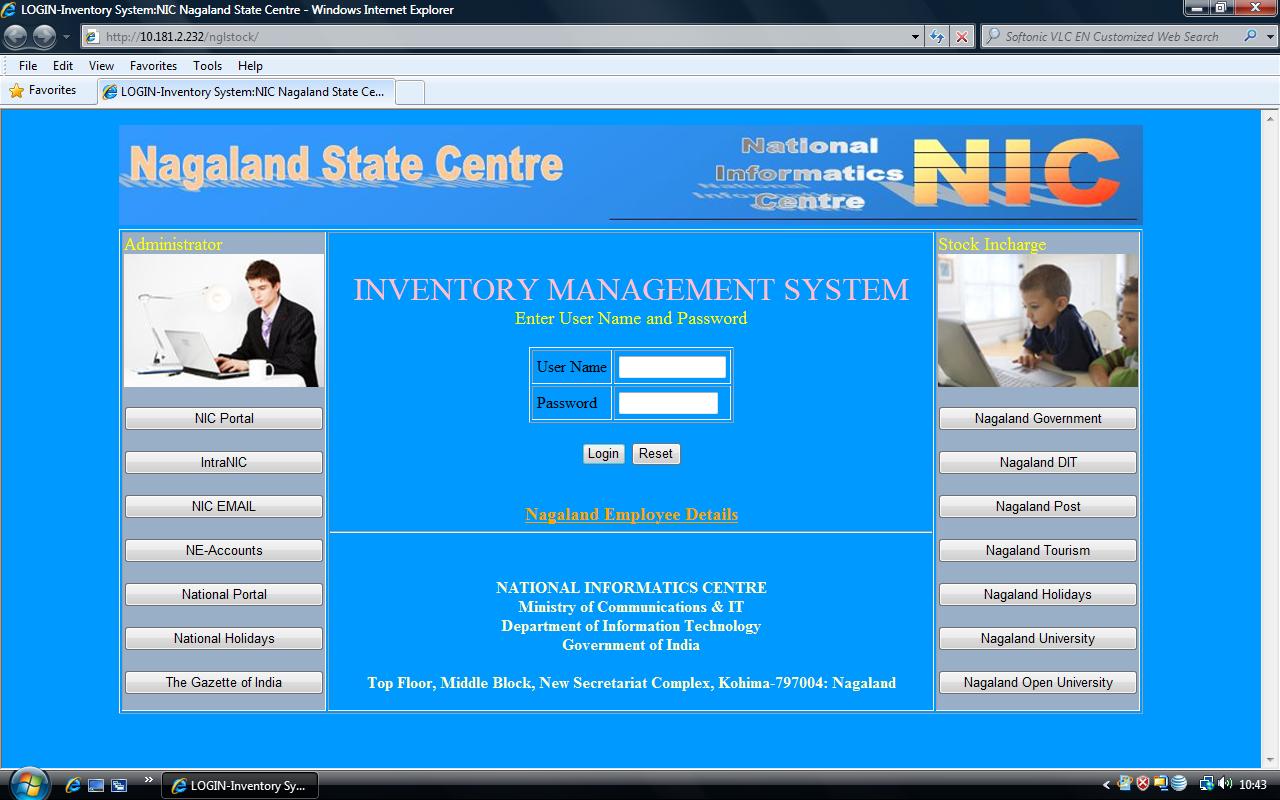
Launching of Online Inventory Management System for NIC Nagaland
The in-house application for Online Inventory Management System developed by NIC Nagaland State Centre for NIC internal use was formally launched by Mr. Kezungulo Medikhru, SIO on 15 November 2010 in the presence of Shri. Vinay Thakur, STD & NE States Coordinator, NIC Hqr. New Delhi and the DIOs...
NIC Orissa State Centre Bhubaneswar shares Liquid Love
There is no gift, more precious than life. And Blood, runs through the very veins of this gift. Also there is no substitute of this gift, the lifeline of human existence. NIC Orissa State Unit in association with the Indian Red Cross Society, organized the voluntary Blood Donation Camp in memory of...




 Subscribe
Subscribe




 Flipbook
Flipbook PDF (4.5 MB)
PDF (4.5 MB)


