News
Haryana: Launching of On Line Entrance Test (OLET)
The On Line Entrance Test for MCA and B.Tech (Leet) was launched for the academic session 2013-14 on 24th April 2013 after taking approval of the Project Evaluation Committee of NIC. The project is jointly implemented by NIC, NICSI & HSTES (Haryana State Technical Educational Society) and a tri-party...
Workshop on eAuction of IMFL OFF Shops held at Training Hall, Watershed, Jharsuguda, Odisha
One day Training Programme for Bidders of Jharsuguda District on eAuction of IMFL ‘OFF’ Shops was conducted on 23/04/2013 at Training Hall, Watershed, Jharsuguda. Shri Uttam Kumar Meher, Superintendent of Excise, Jharsuguda addressed the participants and explained importance of the...
Launching of IVFRT system for Districts of Tamilnadu at Coimbatore on 22/04/2013
Immigration, Visa, Foreigners registration and Tracking (IVFRT) system was launched for Tamil nadu districts at Coimbatore on 22/04/2013. It is a Mission mode National e-Governance project of Govt. of India to provide the high standard of integrated Visa and Immigration services for the visiting foreigners...
Dr Y. K. Sharma, DG, NIC inaugurated DIOs Workshop on eAuction
With the firm decision of Government of Odisha to go ahead with the allotment of licenses of about 1400 IMFL off shops and CS shops through eAuction platform of NIC, a one day workshop was conducted in NIC Bhubaneswar for District Informatics Officers of Odisha on 25th April 2013. The workshop was...
Director General NIC
Shri M. Moni takes over as DG, NIC from 1st May 2013 Shri M Moni, took over the charge from Dr. Y.K. Sharma as the new Director General of NIC on 1st May 2013. In his maiden speech, he expressed his gratitude towards SIOs, DIOs, Informatics officers and all other NIC people for their sincere,...

 Subscribe
Subscribe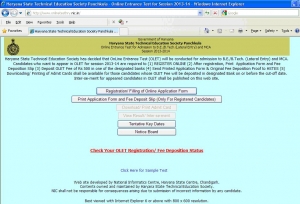





 Flipbook
Flipbook PDF (6.8 MB)
PDF (6.8 MB)